Earlier today, the Wall Street Journal published evidence that Google has been circumventing the privacy settings of Safari and iPhone users, tracking them on non-Google sites despite Apple's default settings, which were intended to prevent such tracking.
This tracking, discovered by Stanford researcher Jonathan Mayer, was a technical side-effect—probably an unintended side-effect—of a system that Google built to pass social personalization information (like, “your friend Suzy +1'ed this ad about candy”) from the google.com domain to the doubleclick.net domain. Further technical explanation can be found below.
Coming on the heels of Google’s controversial decision to tear down the privacy-protective walls between some of its other services, this is bad news for the company. It’s time for Google to acknowledge that it can do a better job of respecting the privacy of Web users. One way that Google can prove itself as a good actor in the online privacy debate is by providing meaningful ways for users to limit what data Google collects about them. Specifically, it’s time that Google's third-party web servers start respecting Do Not Track requests, and time for Google to offer a built-in Do Not Track option.
Meanwhile, users who want to be safe against web tracking can't rely on Safari's well-intentioned but circumventable protections. Until Do Not Track is more widely respected, users who wish to defend themselves against online tracking should use AdBlock Plus for Firefox or Chrome, or Tracking Protection Lists for Internet Explorer.1 AdBlock needs to be used with EasyPrivacy and EasyList in order to offer maximal protection.
Technical details: Google tries to poke a small hole in Safari's privacy protections, but the hole becomes very large
The Safari and iOS browsers have a useful privacy feature: they automatically reject third-party tracking cookies unless a user actively interacts with a widget or clicks on the third party's ads. This is a big step up from the default settings on most browsers. Advertisers typically use tracking cookies to create an invisible record of your online browsing habits, and large advertisers can track you across huge swaths of the web. Safari offers some protection against this type of passive tracking: it specifically prevents a site from setting cookies unless those cookies are from a domain name that you have visited or interacted with directly.
As Google engineers were building the system for passing facts like "your friend Suzy +1'ed this ad" from google.com to doubleclick.net, they would have likely realized that Safari was stopping them from linking this data using third-party DoubleClick cookies. So it appears they added special JavaScript code that tricked Safari into thinking the user was interacting with DoubleClick,2 causing Safari to allow the cookies that would facilitate social personalization (and perhaps, at some point, other forms of pseudonymous behavioral targeting). This was a small hole in Safari's privacy protections.
Unfortunately, that had the side effect of completely undoing all of Safari's protections against doubleclick.net. It caused Safari to allow other DoubleClick cookies, and especially the main "id" tracking cookie that Safari normally blocked. Like a balloon popped with a pinprick, all of Safari's protections against DoubleClick were gone.
The Wall Street Journal has an excellent infographic explaining this process.
The right hand is not talking to the left
Public statements by Google have indicated that parts of the company had a fairly good understanding of Safari's privacy protections:
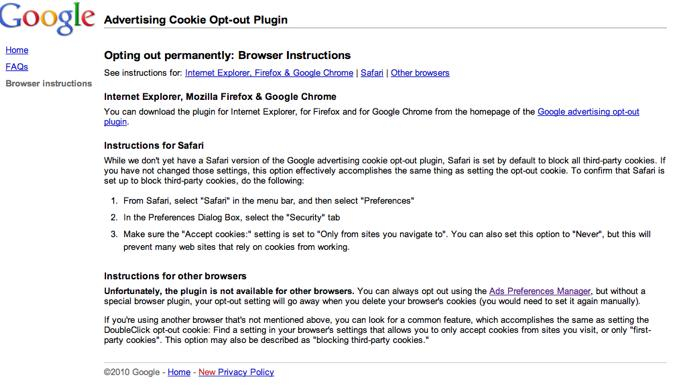
In the screenshot above, Google states: “While we don’t yet have a Safari version of the Google advertising cookie opt-out plugin, Safari is set by default to block all third party cookies. If you have not changed those settings, this option effectively accomplished the same thing as setting the opt-out cookie.” If only that had stayed true.
Safari gives users an opportunity to block passive tracking by online advertisers. Google's decision to route around those settings took it down a dangerous road. Any code that was specifically designed to circumvent privacy protection features should have triggered a much higher level of review and caution, and that clearly did not happen.
Can Advertisers Learn That "No Means No" (PDF), a research study on flash cookies published in 2011, characterized online advertisers who used flash cookies to override user privacy settings as paternalistic:
Advertisers see individuals as objects. When conceived of as objects, consumers’ preferences no longer matter. Privacy can be coded into oblivion or be circumvented with technology. Our 2009 and 2011 work empirically demonstrates that advertisers implement paternalistic judgments that subjects of targeted marketing cannot make proper judgments for themselves.
Today, Google looks just as paternalistic as ad networks setting flash cookies to outfox people who try to delete their cookies.
People around the world rely on Safari to browse the web, including iPhone users, whose choices are severely limited by Apple's walled garden. That’s a lot of people who are denied a voice when it comes to online tracking.
It’s Time for Google to Make Amends: an Open Letter to Google
Google, the time has finally come. You need to make a pro-privacy offering to restore your users’ trust.
Internet users worldwide have loved your products for years, and we’ve often praised your stance on free expression and transparency and your efforts to limit government access to users’ information. But when it comes to consumer choice around privacy, your commitment to users has been weaker. That’s bad for users, for the future of the Internet, and ultimately, for you. We need to create an Internet that gives users meaningful choice about sharing their personal data, and we need your help to do it.
It’s time for a new chapter in Google’s policy regarding privacy. It’s time to commit to giving users a voice about tracking and then respecting those wishes.
For a long time, we’ve hoped to see Google respect Do Not Track requests when it acts as a third party on the Web, and implement Do Not Track in the Chrome browser. This privacy setting, available in every other major browser, lets users express their choice about whether they want to be tracked by mysterious third parties with whom they have no relationship. And even if a user deleted her cookies, the setting would still be there.
Right now, EFF, Google, and many other groups are involved in a multi-stakeholder process to define the scope and execution of Do Not Track through the Tracking Protection Working Group. Through this participatory forum, civil liberties organizations, advertisers, and leading technologists are working together to define how Do Not Track will give users a meaningful way to control online tracking without unduly burdening companies. This is the perfect forum for Google to engage on the technical specifications of the Do Not Track signal, and an opportunity to bring all parties together to fight for user rights. While the Do Not Track specification is not yet final, there's no reason to wait. Google has repeatedly led the way on web security by implementing features long before they were standardized. Google should do the same with web privacy. Get started today by linking Do Not Track to your existing opt-out mechanisms for advertising, +1, and analytics.
Google, make this a new era in your commitment to defending user privacy. Commit to offering and respecting Do Not Track.
- 1. As this blog goes to press, we are unsure whether ad blockers for Safari can prevent the browser from sending requests, which is essential for this kind of privacy protection to be effective.
- 2. The code was web developers call a "hidden form submission", contained in a DoubleClick iframe. This code was only sent to Apple's browsers: Mayer tested 400 user-agent strings, and found that only Safari received the JavaScript that performed hidden form submissions.




