Microsoft has collaborated closely with US intelligence services to allow users’ communications to be intercepted, including helping the National Security Agency to circumvent the company’s own encryption, according to top-secret documents obtained by the Guardian.
The files provided by Edward Snowden illustrate the scale of co-operation between Silicon Valley and the intelligence agencies over the last three years. They also shed new light on the workings of the top-secret Prism program, which was disclosed by the Guardian and the Washington Post last month.
The documents show that:
• Microsoft helped the NSA to circumvent its encryption to address concerns that the agency would be unable to intercept web chats on the new Outlook.com portal;
• The agency already had pre-encryption stage access to email on Outlook.com, including Hotmail;
• The company worked with the FBI this year to allow the NSA easier access via Prism to its cloud storage service SkyDrive, which now has more than 250 million users worldwide;
• Microsoft also worked with the FBI’s Data Intercept Unit to “understand” potential issues with a feature in Outlook.com that allows users to create email aliases;
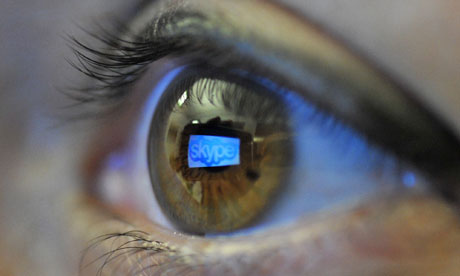
• In July last year, nine months after Microsoft bought Skype, the NSA boasted that a new capability had tripled the amount of Skype video calls being collected through Prism;
• Material collected through Prism is routinely shared with the FBI and CIA, with one NSA document describing the program as a “team sport”.
The latest NSA revelations further expose the tensions between Silicon Valley and the Obama administration. All the major tech firms are lobbying the government to allow them to disclose more fully the extent and nature of their co-operation with the NSA to meet their customers’ privacy concerns. Privately, tech executives are at pains to distance themselves from claims of collaboration and teamwork given by the NSA documents, and insist the process is driven by legal compulsion.
In a statement, Microsoft said: “When we upgrade or update products we aren’t absolved from the need to comply with existing or future lawful demands.” The company reiterated its argument that it provides customer data “only in response to government demands and we only ever comply with orders for requests about specific accounts or identifiers”.
In June, the Guardian revealed that the NSA claimed to have “direct access” through the Prism program to the systems of many major internet companies, including Microsoft, Skype, Apple, Google, Facebook and Yahoo.
Blanket orders from the secret surveillance court allow these communications to be collected without an individual warrant if the NSA operative has a 51% belief that the target is not a US citizen and is not on US soil at the time. Targeting US citizens does require an individual warrant, but the NSA is able to collect Americans’ communications without a warrant if the target is a foreign national located overseas.
Since Prism’s existence became public, Microsoft and the other companies listed on the NSA documents as providers have denied all knowledge of the program and insisted that the intelligence agencies do not have back doors into their systems.
Microsoft’s latest marketing campaign, launched in April, emphasizes its commitment to privacy with the slogan: “Your privacy is our priority.”
Similarly, Skype’s privacy policy states: “Skype is committed to respecting your privacy and the confidentiality of your personal data, traffic data and communications content.”
But internal NSA newsletters, marked top secret, suggest the co-operation between the intelligence community and the companies is deep and ongoing.
The latest documents come from the NSA’s Special Source Operations (SSO) division, described by Snowden as the “crown jewel” of the agency. It is responsible for all programs aimed at US communications systems through corporate partnerships such as Prism.
The files show that the NSA became concerned about the interception of encrypted chats on Microsoft’s Outlook.com portal from the moment the company began testing the service in July last year.
Within five months, the documents explain, Microsoft and the FBI had come up with a solution that allowed the NSA to circumvent encryption on Outlook.com chats
A newsletter entry dated 26 December 2012 states: “MS [Microsoft], working with the FBI, developed a surveillance capability to deal” with the issue. “These solutions were successfully tested and went live 12 Dec 2012.”
Two months later, in February this year, Microsoft officially launched the Outlook.com portal.
Another newsletter entry stated that NSA already had pre-encryption access to Outlook email. “For Prism collection against Hotmail, Live, and Outlook.com emails will be unaffected because Prism collects this data prior to encryption.”
Microsoft’s co-operation was not limited to Outlook.com. An entry dated 8 April 2013 describes how the company worked “for many months” with the FBI – which acts as the liaison between the intelligence agencies and Silicon Valley on Prism – to allow Prism access without separate authorization to its cloud storage service SkyDrive.
The document describes how this access “means that analysts will no longer have to make a special request to SSO for this – a process step that many analysts may not have known about”.
The NSA explained that “this new capability will result in a much more complete and timely collection response”. It continued: “This success is the result of the FBI working for many months with Microsoft to get this tasking and collection solution established.”
A separate entry identified another area for collaboration. “The FBI Data Intercept Technology Unit (DITU) team is working with Microsoft to understand an additional feature in Outlook.com which allows users to create email aliases, which may affect our tasking processes.”
The NSA has devoted substantial efforts in the last two years to work with Microsoft to ensure increased access to Skype, which has an estimated 663 million global users.
One document boasts that Prism monitoring of Skype video production has roughly tripled since a new capability was added on 14 July 2012. “The audio portions of these sessions have been processed correctly all along, but without the accompanying video. Now, analysts will have the complete ‘picture’,” it says.
Eight months before being bought by Microsoft, Skype joined the Prism program in February 2011.
According to the NSA documents, work had begun on smoothly integrating Skype into Prism in November 2010, but it was not until 4 February 2011 that the company was served with a directive to comply signed by the attorney general.
The NSA was able to start tasking Skype communications the following day, and collection began on 6 February. “Feedback indicated that a collected Skype call was very clear and the metadata looked complete,” the document stated, praising the co-operation between NSA teams and the FBI. “Collaborative teamwork was the key to the successful addition of another provider to the Prism system.”
ACLU technology expert Chris Soghoian said the revelations would surprise many Skype users. “In the past, Skype made affirmative promises to users about their inability to perform wiretaps,” he said. “It’s hard to square Microsoft’s secret collaboration with the NSA with its high-profile efforts to compete on privacy with Google.”
The information the NSA collects from Prism is routinely shared with both the FBI and CIA. A 3 August 2012 newsletter describes how the NSA has recently expanded sharing with the other two agencies.
The NSA, the entry reveals, has even automated the sharing of aspects of Prism, using software that “enables our partners to see which selectors [search terms] the National Security Agency has tasked to Prism”.
The document continues: “The FBI and CIA then can request a copy of Prism collection of any selector…” As a result, the author notes: “these two activities underscore the point that Prism is a team sport!”
In its statement to the Guardian, Microsoft said:
We have clear principles which guide the response across our entire company to government demands for customer information for both law enforcement and national security issues. First, we take our commitments to our customers and to compliance with applicable law very seriously, so we provide customer data only in response to legal processes.
Second, our compliance team examines all demands very closely, and we reject them if we believe they aren’t valid. Third, we only ever comply with orders about specific accounts or identifiers, and we would not respond to the kind of blanket orders discussed in the press over the past few weeks, as the volumes documented in our most recent disclosure clearly illustrate.
Finally when we upgrade or update products legal obligations may in some circumstances require that we maintain the ability to provide information in response to a law enforcement or national security request. There are aspects of this debate that we wish we were able to discuss more freely. That’s why we’ve argued for additional transparency that would help everyone understand and debate these important issues.
In a joint statement, Shawn Turner, spokesman for the director of National Intelligence, and Judith Emmel, spokeswoman for the NSA, said:
The articles describe court-ordered surveillance – and a US company’s efforts to comply with these legally mandated requirements. The US operates its programs under a strict oversight regime, with careful monitoring by the courts, Congress and the Director of National Intelligence. Not all countries have equivalent oversight requirements to protect civil liberties and privacy.
They added: “In practice, US companies put energy, focus and commitment into consistently protecting the privacy of their customers around the world, while meeting their obligations under the laws of the US and other countries in which they operate.”
–
• This article was amended on 11 July 2013 to reflect information from Microsoft that it did not make any changes to Skype to allow Prism collection on or around July 2012.